Open source research for accountability & justice
Open source research is gaining momentum for justice and accountability work. Open source research is more and more used in legal cases to support investigations. Technology and widely available online information have made it possible to complement investigations on on-going cases.
Becoming more and more recognised in court rooms, OSINT research processes have been studied and tested for legal applications. Berkeley university has published an OSINT research protocol, Berkeley Protocol on Digital Sources Investigation, giving guidance on using public digital info to fight for human rights.
Some accountability OSINT projects have become inspirational: Syria Archives, Yemen Archives , Myanmar Witness or CIR Russian-Ukraine monitoring map.
Definition
We are using the term « mercenaries » to refer to the Wagner Group as understood in article 47 of the additional Protocol I to the Geneva Convention:
- who is specially recruited domestically or abroad to fight in an armed conflict;
- who in fact takes a direct part in hostilities;
- who takes part in hostilities primarily with a view to obtaining a personal advantage and who is actually promised, by a party to the conflict or on its behalf, material remuneration significantly higher than that promised or paid to combatants of a rank and function analogues in the armed forces of this party;
- who is neither a national of a party to the conflict nor a resident of the territory controlled by a party to the conflict;
- who is not a member of the armed forces of a party to the conflict; and who has not been sent by a State other than a party to the conflict on official mission as a member of the armed forces of that State.
Our investigative approach
We follow the research process described by the Berkeley Protocol and used by most.
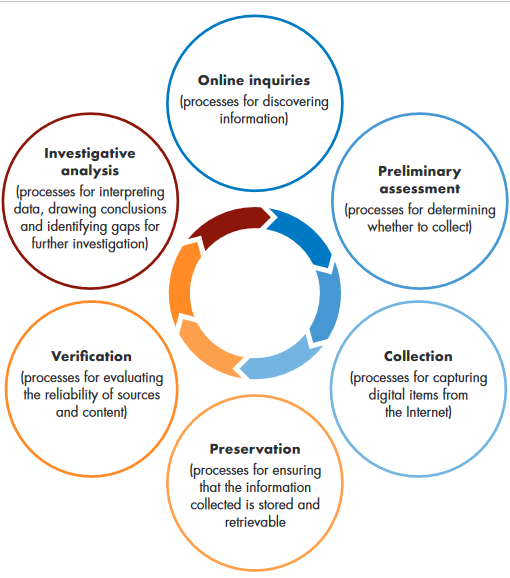
Online inquiries: All Eyes on Wagner combines online open source research and information securily transferred to the project members through secure email and platform.
Preliminary assessment: The project focuses on very specific research areas linked to Wagner group’s activities. Claims related to research areas are systematically collected for verification.
Collection: 1) Visual content is primarily accessed through social media channels (Twitter, Facebook, VK, Websites, Telegram, etc), transferred files (videos, photos, pdf), and external and members’ documents or data sets. 2) Claims are collected from sources identified as credible: local media, NGOs, International Organisations, journalists, etc. 3) A standardised metadata scheme is applied to each content after it has been preserved and includes basic information such as title, location, media type, research area, abuse type.
Preservation: The project’s collection and secure preservation workflow ensures that original content is not lost due to its removal and can be used later on by other organisations in an accountability context. Digital content is archived online on websites such as the Internet archive and is stored on a project platform, as well as on hard drives. Digital content is then hashed and timestamped.
Verification: Digital content is verified by trying to answer the who, what, where, when, from who and how questions using open sources.
Investigative analysis: In some cases, in-depth open-source investigations are conducted. Some case studies and long reads will be published on this website.